Webhooks are just HTTP requests from an unknown source, so verifying the authenticity of webhooks is a requirement for any secure webhook implementation.Documentation Index
Fetch the complete documentation index at: https://docs.connect.fastenhealth.com/llms.txt
Use this file to discover all available pages before exploring further.
Retrieving your endpoint’s secret
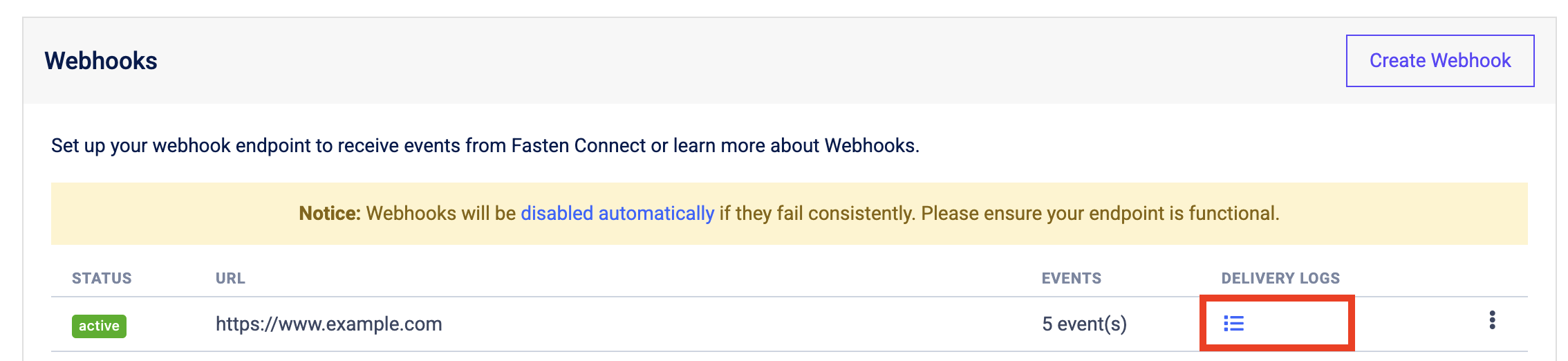
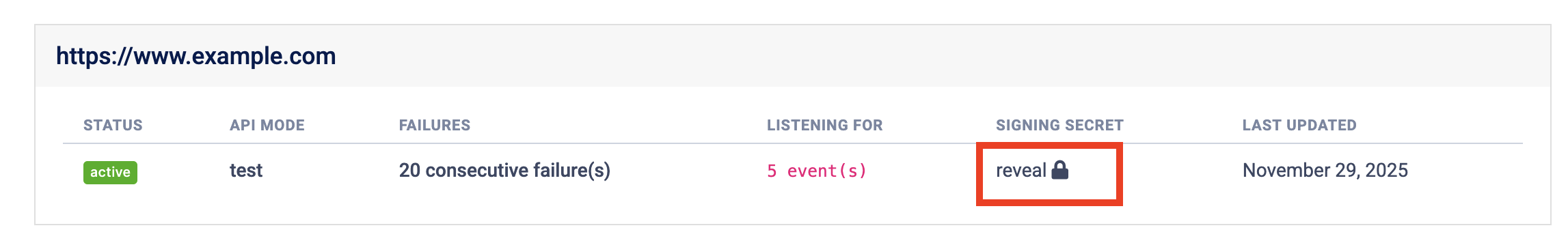
Find the Webhooks section of the Developer Portal. Click theDeveloper Logs for the endpoint that you want
to obtain the secret for, and find the Signing Secret on the top right of the Delivery Logs page.
Preventing replay attacks
A replay attack is when an attacker intercepts a valid payload and its signature, then re-transmits them. To mitigate such attacks, Fasten Connect includes a timestamp in theWebhook-Signature header. Because this timestamp is part of the signed payload,
it’s also verified by the signature, so an attacker can’t change the timestamp without invalidating the signature.
If the signature is valid but the timestamp is too old, you can have your application reject the payload.
Fasten Connect generates the timestamp and signature each time we send an event to your endpoint. If Fasten Connect retries an
event (for example, your endpoint previously replied with a non-200 status code), then we generate a new signature and timestamp for the new delivery attempt.
Verification
Fasten Connect webhooks conform to the Standard-Webhooks specification, which means that you can use any of the libraries that implement the specification to verify the webhook signatures. See the Standard-Webhooks libraries page for a list of libraries that you can use to verify webhook signatures.

